Dear customers,
Several media across Europe reported an increased number of unsuccessful access attempts to FRITZ!Box modems. Edpnet has taken the necessary measures to avoid possible attempts and mitigate the risk for our customers.
The access attempts are usually automated and originate from unknown remote sites on the internet, using common user names and passwords, and are known as brute-force attacks.
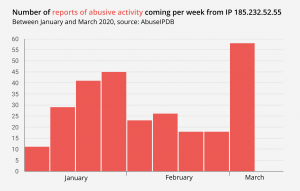
The recent wave of attacks was originated from the IP address 185.232.52.55 which, according to AbuseIPDB, has been involved in multiple abusive activities for quite a while now. Our NOC team denied all traffic from this IP address to our network, which will make further attacks impossible.
Generally these attacks are not something to worry about, as hackers rely on password stuffing (a systematic attempt at guessing all possible combinations in a particular character space), which, as long as the device is protected by a strong and unique password, does not appear to carry any significant risk for users.
FRITZ!Box has its own built-in brute-force protection system which notably reduces the risk of a successful intrusion. Those FRITZ!Box devices over which we have a remote control via the protocol TR-069 are also secure: we use automatically generated users and passwords which are virtually impossible to guess. Apart from that, our team is on standby 24/7 to blackhole the IP addresses which are engaged in abusive activities should a new massive attack happens.
The situation has also been acknowledged by AVM, the manufacturer of FRITZ! products. To make it more difficult for unauthorized persons to access your FRITZ!Box and to minimize the number of weak points for potential attacks, check out the following safety instructions: https://en.avm.de/service/fritzbox/fritzbox-7360/knowledge-base/publication/show/3299_FRITZ-Box-reports-Login-by-user-failed/
If you have any questions left, please do not hesitate to contact us.
Best regards
The edpnet team