Belgium / Maintenance / Planned /
Dear customers,
please be informed that the maintenance we announced earlier for Bruxelles (postcode 1000) has been rescheduled for 07/07/2022.
Please check the new maintenance window below:
| Start*: |
07-07-2022 00:00 |
| End*: |
07-07-2022 07:15 |
| Duration: |
expected impact: 15 minutes |
| Impacted services: |
all internet services |
| Affected Areas**: |
Bruxelles (1000) |
We apologize for the inconveniences.
Best regards
The edpnet team
* All times are listed in CET, Central European Time
** Check the different areas & zones on our support site
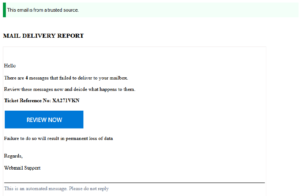
Belgium / Netherlands / Phishing /
Dear customers,
We would like to inform you about a new phishing wave that is aimed at both customers and non-customers.
Customers receive emails with a fake delivery notice, pretending to come from edpnet and containing a phishing link.
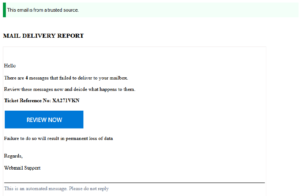
Please do not reply to those emails and do not click on the link. For more information, please, consider reading through our support article on this subject
https://www.edpnet.be/en/support/troubleshooting/internet/learn-about-security/phishing.html
If you have any questions left, please do not hesitate to contact us.
Best regards
The edpnet team
Belgium / Brussels / Maintenance / Planned /
Dear customers,
Proximus has planned a maintenance which may affect your services.
Please find all details below:
| Start*: |
04-07-2022 00:00 |
| End*: |
04-07-2022 07:15 |
| Duration: |
expected impact: 15 minutes |
| Impacted services: |
all internet services |
| Affected Areas**: |
Bruxelles (1000) |
We apologize for the inconveniences.
Best regards
The edpnet team
* All times are listed in CET, Central European Time
** Check the different areas & zones on our support site
Belgium / Info / Maintenance / Planned /
Dear customers,
Proximus has planned a maintenance which may affect your services.
Please find all details below:
| Start*: |
28-06-2022 08:00 |
| End*: |
28-06-2022 16:30 |
| Duration: |
potential impact: 15 minutes |
| Impacted services: |
all internet services |
| Affected Areas**: |
La Louvière |
We apologize for the inconveniences.
Best regards
The edpnet team
* All times are listed in CET, Central European Time
** Check the different areas & zones on our support site
Maintenance / Netherlands / Planned /
Dear customers,
Please be informed that the maintenance we announced earlier for the Netherlands has been postponed to 28/06/2022.
This maintenance will cause multiple short disconnections during the scheduled window.
Please find all details below:
| Start*: |
28/06/2022 00:00 |
| End*: |
28/06/2022 06:00 |
| Duration: |
expected impact: multiple short disruptions |
| Impacted services: |
all internet services |
| Affected Areas**: |
the Netherlands: all areas |
We apologize for the inconveniences.
Best regards
The edpnet team
* All times are listed in CET, Central European Time
** Check the different areas & zones on our support site
Info / Maintenance / Netherlands / Planned /
Dear customers,
We have planned a maintenance on our core routers in order to improve the performance and the quality of our services.
The maintenance will cause multiple short disconnections during the scheduled window.
Please find all details below:
| Start*: |
27-06-2022 00:00 |
| End*: |
27-06-2022 06:00 |
| Duration: |
expected impact: multiple short disruptions |
| Impacted services: |
all internet services |
| Affected Areas**: |
the Netherlands: all areas |
We apologize for the inconveniences.
Best regards
The edpnet team
* All times are listed in CET, Central European Time
** Check the different areas & zones on our support site
Belgium / Info / Maintenance / Planned /
Dear customers,
Proximus has planned a maintenance which may affect your services.
Please find all details below:
| Start*: |
17-06-2022 00:00 |
| End*: |
17-06-2022 06:00 |
| Duration: |
6 hours |
| Impacted services: |
all internet services |
| Affected Areas**: |
La Louvière |
We apologize for the inconveniences.
Best regards
The edpnet team
* All times are listed in CET, Central European Time
** Check the different areas & zones on our support site
Belgium / Info / Maintenance / Planned /
Dear customers,
We have planned a maintenance on our core routers in order to improve the performance and the quality of our services.
These works may cause a short interruption of your connection during scheduled maintenance window.
Please find all details below:
| Start*: |
07-06-2022 03:00 |
| End*: |
07-06-2022 05:00 |
| Duration: |
potential impact: possible loss of connection during the maintenance window |
| Impacted services: |
all internet services |
| Affected Areas**: |
all areas |
We apologize for the inconveniences.
Best regards
The edpnet team
* All times are listed in CET, Central European Time
** Check the different areas & zones on our support site
Belgium / Info / Maintenance / Planned /
Dear customers,
Proximus has planned a maintenance in order to move some underground cables before the road works.
This maintenance may affect your services.
Please find all details below:
| Start*: |
16-06-2022 00:05 |
| End*: |
16-06-2022 06:00 |
| Duration: |
5 hours 55 minutes |
| Impacted services: |
all internet services |
| Affected Areas**: |
Herentals |
We apologize for the inconveniences.
Best regards
The edpnet team
* All times are listed in CET, Central European Time
** Check the different areas & zones on our support site
Belgium / Info / Maintenance / Planned /
Dear customers,
Proximus has planned a maintenance which may affect your services.
Please find all details below:
| Start*: |
20-05-2022 00:00 |
| End*: |
20-05-2022 06:00 |
| Duration: |
6 hours |
| Impacted services: |
all internet services |
| Affected Areas**: |
La Louvière |
We apologize for the inconveniences.
Best regards
The edpnet team
* All times are listed in CET, Central European Time
** Check the different areas & zones on our support site